A client asked me a simple question recently, “Are we at the highest possible security level?”
It’s a fair question, and an important one. But the answer, in this case, wasn’t what they expected.
For perspective, it’s important to note that Web Propulsion does not manage this client’s web hosting. Their hosting is packaged with a “full-service” web development company. We do manage the client’s domain and DNS services however.
After reviewing their account, here’s what we found:
- Their domain and DNS are securely managed by Web Propulsion Hosting on the Cloudflare platform. Our client has full access. (a strong, secure foundation)
- Their WordPress website is hosted by their web development/marketing agency with a hosting company headquartered overseas. In this scenario, the hosting relationship is between the hosting company and the marketing agency, not the business owner.
- The business owner does not have direct access to the hosting platform.
- The business owner does not have full WordPress administrator privileges (no access to install plugins, no capability to perform backups)
From a distance, everything looked “fine.” But from a security standpoint? Our review exposed security risks our client had not yet considered.
The Illusion of Security
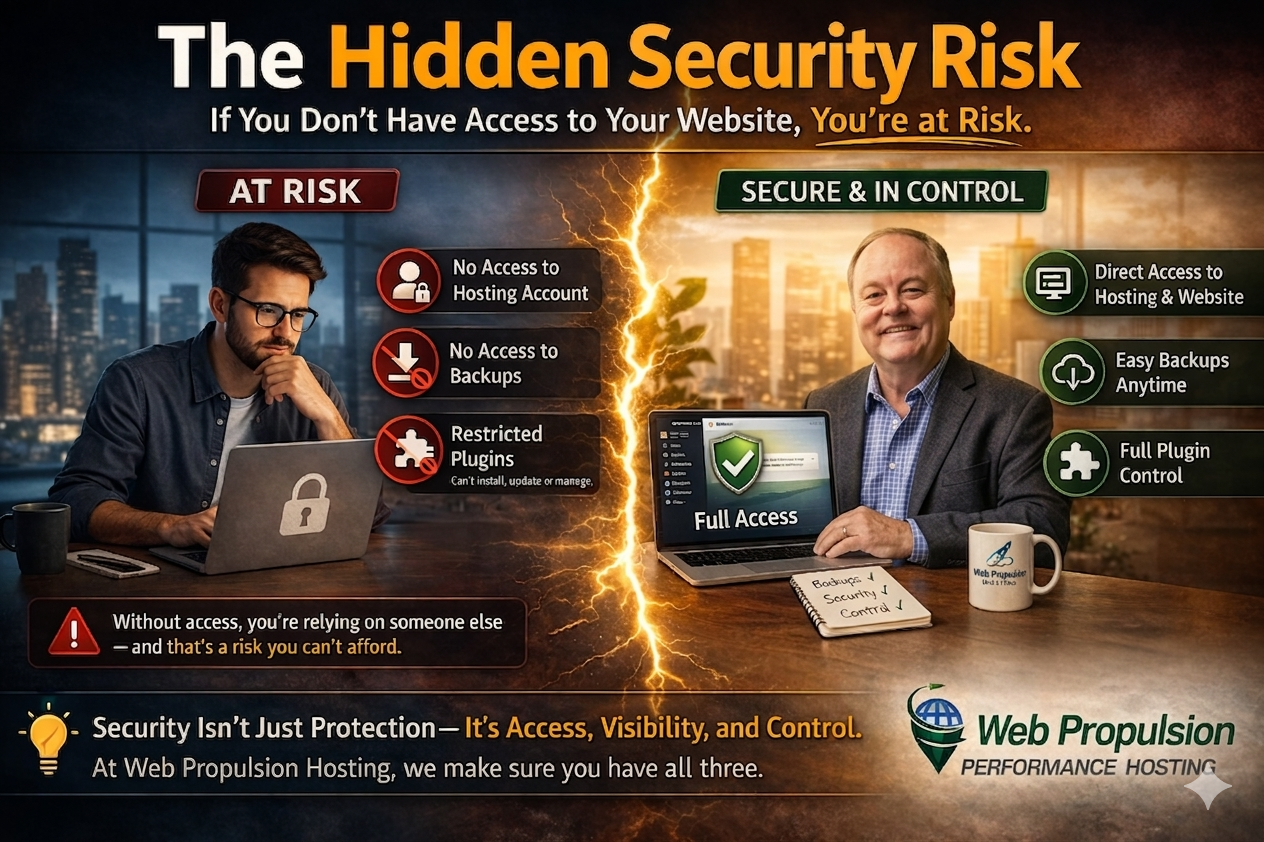
Security isn’t just about firewalls, malware scans, or SSL certificates. Security is also about access and control. If you don’t have full access to your website and your hosting account, you don’t have true security, you have third-party dependency.
Let’s Break Down the Risk in this Scenario.
1. No Direct Hosting Access
If you cannot log in to the hosting account where your website is hosted, then:
- You cannot verify backups
- You cannot review server-level security
- You cannot respond quickly in an emergency
- You cannot move your website if needed
This creates a single point of failure: the agency who controls the relationship with the hosting company.
If they disappear, delay, or make a mistake, you could be locked out of your own business asset, your company website, and in some cases your domain.
2. No Ability to Run Backups
This is one of the most critical risks.
If you cannot:
- Install a backup plugin
- Run a manual backup
- Download a copy of your website
Then you are relying entirely on someone else to protect your data.
And here’s the hard truth:
If you don’t control your backups, you don’t control your recovery.
Whether it’s a hack, plugin conflict, or accidental deletion, recovery becomes uncertain, slow, or impossible.
3. Restricted WordPress Access (No Plugin Control)
When plugin access is restricted, the business owner does not have full WordPress access:
- You cannot install security tools
- You cannot install backup solutions
- You cannot audit what’s running on your site
- You cannot remove outdated or vulnerable plugins
This means:
You cannot independently verify your own website’s security posture.
You are forced to trust without visibility.
4. Developer/Agency Controlled Infrastructure
Most agencies excel at what they do, design, development, and marketing, and play a critical role in helping businesses grow. A WordPress developer or digital marketing agency is often essential to helping your business build and manage your website.
However, domain management, DNS, and web hosting fall outside the scope of marketing, they are part of your underlying business infrastructure, specifically Information Technology (IT) infrastructure.
Where problems often arise is when all aspects of the website environment—hosting, access credentials, backups, and administrative control—are managed as marketing functions rather than IT/infrastructure functions.
Separating domain management, DNS, and web hosting from website management and marketing helps ensure a business maintains full, independent control of its website as a critical business asset.
What “High Security” Actually Looks Like
Regardless of where your website is hosted, here’s what we recommend:
✅ You have direct access to your hosting account
✅ You have full administrative access to WordPress
✅ You can run and download backups at any time
✅ Your domain and DNS are managed on a secure, reliable platform like Cloudflare
✅ Your hosting provider is transparent about their security practices
Conclusion: Security You Can See, Understand, and Control
At Web Propulsion Hosting, we believe security isn’t something that should be hidden behind a curtain, it should be something you can see, understand, and actively participate in.
Our approach is simple:
- You have full visibility into your hosting environment
- You have direct access to your hosting tools and WordPress platform
- You’re never left guessing about how your website works
We don’t just “handle things” for you, we walk alongside you.
That means:
- Showing you how to generate and download your own backups
- Explaining what your hosting environment is doing behind the scenes
- Helping you understand why certain security measures matter
- Being available when you need real answers, not generic support tickets
Because in our experience, the most secure clients aren’t the ones kept in the dark…
They’re the ones who are informed, empowered, and supported by real people.
After 25+ years in this industry, we’ve learned that technology alone doesn’t create security, relationships do.
And when you combine the right infrastructure with human expertise and transparency, that’s where real security begins.